As an internet-connected device, your phone can be vulnerable to cybercrime. Hackers and cybercriminals may attempt to secretly access your device to steal valuable information like your bank account number, email address, and more.
Despite this serious threat, many people do not know how to secure their phones from hackers. This is understandable, as a quick Google search of the phrase “secure phone from hackers” will yield hundreds of results and a lot of conflicting information.
Below, we will provide some tell-tale signs that your phone has been hacked, as well as proven tips for preventing it from happening in the first place.
How to Secure Phone from Hackers
Unfortunately, there is no way to make your phone 100% secure from hackers. However, there are plenty of ways to protect your phone and the personal data that it contains.
Virtually every mobile device contains basic cybersecurity software that is designed to keep your data safe. These built-in security solutions include password managers, strong password generators, and face ID capabilities.
With that being said, hackers are becoming increasingly sophisticated and can often circumvent these out-of-the-box solutions. That is why you should take additional steps to protect your device (which we will touch on later).
How to Know If Someone Is Hacking Your Phone
Before we delve into all the ways that you can better protect your device, let’s discuss how you can tell if someone is hacking your phone. If you observe any of the following signs, then there is a good chance your phone is being hacked.
Your Phone Runs and Charges Slowly
Perhaps the most common indicator that your phone is being hacked is that it begins to run and charge much slower. While phones will gradually experience a decrease in performance as they age, newer devices should operate at optimal levels.
If your device suddenly begins to charge extremely slowly or has difficulties running basic apps, then it might have been breached.
Once you notice this reduction in performance, be on the lookout for other indicators of hacking. If you observe additional signs, then you may want to replace your device.
You Observe Strange Activity
Another major clue that your phone has been the victim of a data breach is strange activity on any of your accounts. This may include social media pages, bank accounts, or any other platforms that you access through a mobile app.
Remember, if a hacker breaches your personal data, they may be able to log in to all of your accounts, especially if you use the same password repeatedly.
You Begin Receiving Unusual Calls or Messages
While just about everyone receives the occasional robocall, these should not become an everyday occurrence. If you notice an uptick in the frequency of robocalls or begin receiving unusual text messages from strange numbers, then you may have been hacked.
Whatever you do, don’t reply to any of these messages or provide callers with personal information. Some of these bad actors may pretend to be customer service personnel from online retailers, banks, or other companies.
In these scams, the caller will attempt to trick you into providing confidential information, such as your Social Security number, bank account number, or credit card number.
If you have already fallen victim to these scams, deactivate any affected cards and freeze your accounts immediately. This will help you reduce the impact of any acts of fraud and protect your assets.
Tips to Help Secure Phone from Hackers
If you want to better protect your sensitive data, we recommend that you:
Add Biometric Security
Biometric security is included as a standard feature on most mobile devices. The most common types of biometric security include face ID and fingerprint authentication. Both iPhones and Android phones have adopted these technologies.
Biometric security adds an extra layer of protection and is particularly useful for guarding against data breaches in the event your device is stolen. While a thief may be able to guess your four- or six-digit pin, the biometric security will usually stop them in their tracks.
We suggest securing individual applications with biometric security as well. For instance, online payment apps, your mobile banking app, and other software may include the option to enable face ID or fingerprint authentication.
If they do, make sure you turn these features on. This will make it much harder for individuals to access the contents of your phone if it’s lost or stolen.
Use a VPN
Like most people, you probably browse the internet using public WiFi on a regular basis. Whether you are at your favorite coffee shop, the library, or a hotel, free WiFi can be incredibly convenient, especially if your phone plan includes a monthly data limit.
However, using public WiFi increases the risk that you will be the victim of a cyber-attack. Cybercriminals can hack into these public networks and access the data on devices that are connected to them, such as your phone.
While we are certainly not telling you to stop using public WiFi, we do recommend that you use this amenity more cautiously. Specifically, you should download a VPN or virtual private network.
A VPN creates a private network that allows you to confidentially send and receive data across public WiFi networks.
There are a multitude of VPN applications available on the App Store or the Google Play Store. Most of these apps require a monthly or annual subscription, but that is a small price to pay for protecting your personal data.
Backup Your Data Regularly
It is important that you back up your files on a regular basis. Most phone providers and manufacturers offer a certain amount of free cloud storage. If you have exceeded this limit, you can easily purchase more storage capacity for a few dollars per month.
If your phone is hacked and you have to completely wipe it, then you will have to use this backup data to retrieve all of your vital information. The longer you wait between backups, the more data you will lose in the event of a breach.
With this in mind, we suggest performing a backup nightly to ensure you never lose more than 24 hours of data if your phone is lost, stolen, damaged, or hacked.
Delete Unnecessary Apps and Files
Does your phone contain dozens of apps that you have not opened in weeks or even months? If so, then you should go through and delete all of these unused apps. Outdated or discontinued apps may not be receiving regular updates from the developers, which means that they make your phone vulnerable to cyberattacks.
Deleting unnecessary apps and files will also free up storage space, which will reduce the size of your data backups. As a result, you may not have to purchase additional cloud storage to support your regular data backups.
Only Download Official Apps
One of the worst mistakes that you can make is to download apps that are not on the App Store or Google Play Store. These pieces of software may include hidden app permissions that are designed to access your personal data and relay it to third-party entities.
Even if third-party apps were not designed to hack your phone, they may not adhere to the standards set by the App Store or Google Play Store. This means that they might make your phone more vulnerable to being hacked.
If you cannot find a particular app on an official app store, there is a good reason. Keep your sensitive data secure and stick with reputable apps.
Learn How to Remotely Wipe Your Phone
While remote hacking certainly poses a real threat to your personal data, it is not the only danger that you must guard against. You should also take steps to protect your sensitive data in the event your phone is stolen or lost. While apps like Find My iPhone can help you recover your device, this may not always be the case.
If you cannot locate your lost or stolen phone, then you should remotely wipe it. The exact steps for remotely wiping your phone will vary depending on the type of device. However, it typically involves logging into your Apple or Google account from another internet-connected device.
Once you are logged in, the rest of the process should only take a few moments.
We recommend wiping your device as soon as you realize it is missing and have exhausted all attempts to locate it. This reduces the chances that someone will be able to access your personal data.
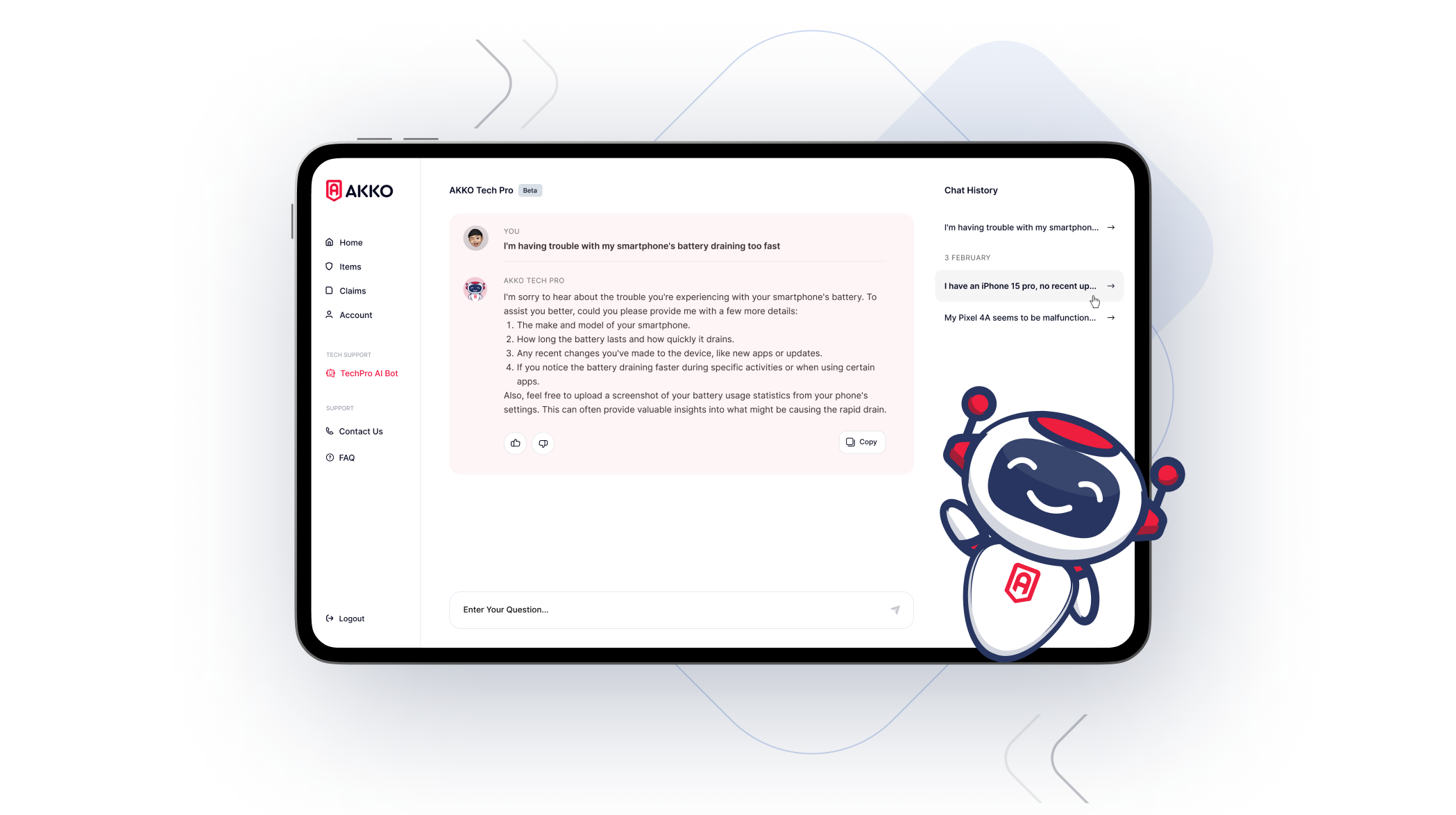
AKKO: Ultimate Device Protection
Now that you have read our tips, you can stop searching the phrase “secure phone from hackers” and proactively protect your device from cyberthreats.
With that being said, none of these tactics are full proof. Despite your best efforts, a wily hacker may still be able to access your phone. When that happens, you will need to wipe your device and replace it.
Typically, replacing your phone can be expensive, especially if you are using a traditional device insurance plan like the ones offered by your provider. Fortunately, the AKKO individual and family plans offer ultimate device protection, even if your device has been compromised by a hacker.
Want to see how our plan stacks up against other top device protection programs? If so, then check out these head-to-head comparisons.
As you can see, AKKO’s plans offer superior protection. Get one of our phone protection plans today and sign up for the last protection plan you’ll ever need.